Cyber Security Firm Discovers Lazarus Group’s New Malware Attack Strategy
Please note that we are not authorised to provide any investment advice. The content on this page is for information purposes only.
Cyber security experts at ESET have uncovered an undocumented cyberattack backdoor, ‘LightlessCan,’ employed by the Lazarus group to target a Spanish aerospace company for espionage.
The new attack strategy is stealthiness-driven and can evade real-time monitoring and digital forensic tools, which may permeate the crypto space and cause colossal losses if not curbed.
ESET Case Study: Operation DreamJob
In a public report on September 29, ESET researchers disclosed a groundbreaking discovery regarding the tactics employed by cyber attackers connected with the Lazarus group.
#ESET researchers unveiled their findings about an attack by the North Korea-linked #APT group #Lazarus that took aim at an aerospace company in Spain.
▶️ Find out more in a #WeekinSecurity video with @TonyAtESET. pic.twitter.com/M94J200VQx
— ESET (@ESET) September 29, 2023
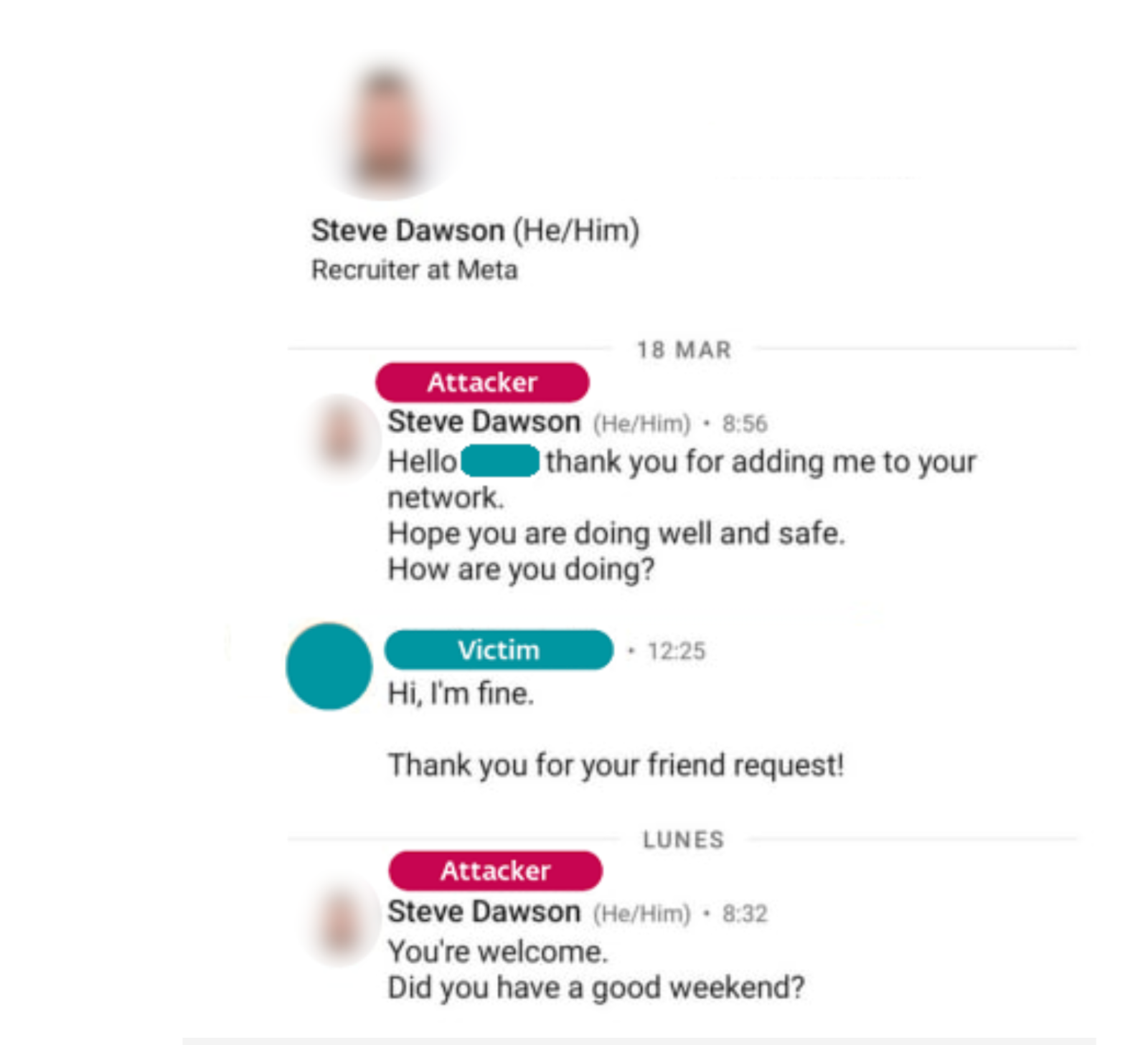
The published research uncovered the group’s deceptive recruitment scheme, where they posed as Meta recruiters to entice unsuspecting employees of a Spanish aerospace firm via LinkedIn with a fabricated job opportunity.
https://twitter.com/ESET/status/1707707211714064653?s=20
This operation, identified as “Operation DreamJob,” entailed victims being directed to download a counterfeit “job file” to access the full job offer details.
In this case, the Lazarus group used the narrative of proving the victim’s proficiency in C++ programming language.
Victims received two malicious executables known as Quiz1.exe and Quiz2.exe, distributed via .iso images hosted on a third-party cloud storage platform.
The first task consisted of a single line of code, while the second generated a Fibonacci sequence.
However, the attackers had a more sinister motive, as both executables were designed to self-compromise the target’s office systems by creating a passage loop.
After the output was printed, both executables triggered the malicious action of installing more payloads from the ISO images into victims’ systems, which created a backdoor for hackers to conduct undetectable espionage.
Peter Kálnai, the ESET researcher who made the discovery, stated that the most worrying aspect of the new attack pathway is the creation of LightlessCan, a complex payload type.
The LightlessCan is an evolving tool that exhibits a high level of advancement in malicious capabilities compared to its predecessor, BlindingCan.
With LightlessCan, hackers have a significant advantage in stealthiness, as it can limit traces of Windows command-line programs, avoid EDRs’ real-time monitoring solution, and postmortem digital forensic tools.
The hackers accessed the Spanish aerospace network through a successful “Operation DreamJob” spearphishing campaign.
While this new strategy may be intended for pure espionage, security experts believe that the biggest crypto space loophole is just a few modifications away.
North Korea Threat Actor & Its Three Pillars of Cybercriminal Activities
The Lazarus group, reportedly linked to North Korea, has been in operation since 2009 and has consistently targeted a wide range of sectors and organizations.
According to the ESET investigative report, the hacker group’s activities can be categorized into three major cybercriminal activities – cyber espionage, cybersabotage, and financial gain.
While aerospace companies aren’t typically the primary targets for this North Korea-affiliated cyber attack group, the recent attack on the Spanish aerospace firm was geared towards cyber espionage.
Last year, researchers from Google and Symantec published an investigative report about a North Korean hack campaign where scammers posted as recruiters from Google, Disney, and Oracle.
According to Adam Weidemann from Google’s Threat Analysis Group, job emails from the scammers contained links that spoofed legitimate job search websites like ZipRecruiter and Indeed.
On July 28, Securonix Threat Research cited that the Lazarus group used fake United States military job-recruitment documents to lure people into downloading malware.
These viruses were staged as legitimate on compromised South Korean e-commerce websites. The crypto space also had its share of attacks, which led to losses of assets and funds.
According to Crystal Blockchain report, $16.7 billion in cryptocurrencies has been stolen in the crypto space between January 2011 and February 2023, with the majority orchestrated by the Lazarus group.
On September 11, blockchain security platform CertiK stated that the group was associated with the $41 million hack from stake online.
We are seeing a further movement of funds from the Stake exploiter.
520k MATIC was swapped and bridged to Avalanche before being bridged to BTC as per other fund movements from the exploiter.
See more on Skynet 👇https://t.co/Sdsfh29AoF
— CertiK Alert (@CertiKAlert) September 11, 2023
Twelve days after the stake attack, the Huobi exchange network was breached, resulting in the theft of 5,000 ETH worth approximately $7.9 million.
🚨Red Code🚨Yesterday, our ML-powered system detected a suspicious transaction involving @HuobiGlobal and @HTX_Global.
Despite our attempts to reach out, we received no response. An EOA received 5K $ETH $7.9M from @HuobiGlobal's hot wallet.🔍 This morning, we spotted… pic.twitter.com/3oqHhAVi8P
— 🚨 Cyvers Alerts 🚨 (@CyversAlerts) September 25, 2023
Although no evidence connects the North Korean threat actor to Huobi attacks, experts believe further investigation will expose the fingerprints of the hacker’s group.